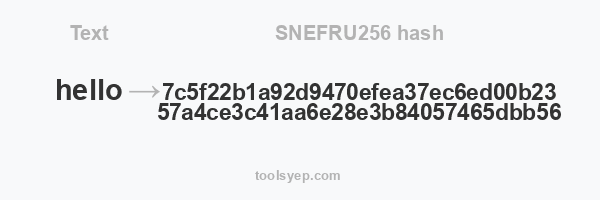
This online tool allows you to generate the hash snefru256 of any string.
SNEFRU256 length is 64 characters
Hash available
MD2 Hash, MD4 Hash, MD5 Hash, SHA1 Hash, SHA224 Hash, SHA256 Hash, SHA384 Hash, SHA512/224 Hash, SHA512/256 Hash, SHA512 Hash, SHA3-224 Hash, SHA3-256 Hash, SHA3-384 Hash, SHA3-512 Hash, RIPEMD128 Hash, RIPEMD160 Hash, RIPEMD256 Hash, RIPEMD320 Hash, WHIRLPOOL Hash, TIGER128,3 Hash, TIGER160,3 Hash, TIGER192,3 Hash, TIGER128,4 Hash, TIGER160,4 Hash, TIGER192,4 Hash, SNEFRU Hash, SNEFRU256 Hash, GOST Hash, GOST-CRYPTO Hash, ADLER32 Hash, CRC32 Hash, CRC32B Hash, CRC32C Hash, FNV132 Hash, FNV1A32 Hash, FNV164 Hash, FNV1A64 Hash, JOAAT Hash, HAVAL128,3 Hash, HAVAL160,3 Hash, HAVAL192,3 Hash, HAVAL224,3 Hash, HAVAL256,3 Hash, HAVAL128,4 Hash, HAVAL160,4 Hash, HAVAL192,4 Hash, HAVAL224,4 Hash, HAVAL256,4 Hash, HAVAL128,5 Hash, HAVAL160,5 Hash, HAVAL192,5 Hash, HAVAL224,5 Hash, HAVAL256,5 Hash,
What is SNEFRU256 hash?
SNEFRU256 is a cryptographic hash function that was developed by Y. Yang, J. H. Cheon, and Y. H. Han in 1998. It is a 256-bit hash function that is designed to be fast and secure.
A hash function is a mathematical function that takes an input (called a "message") and produces a fixed-size output (called a "hash value" or "digest"). The output is usually represented as a hexadecimal string. Hash functions are used in many different applications, including password storage, data integrity checks, and generating unique identifiers.
The SNEFRU256 hash function operates by taking an input message and processing it through a series of mathematical operations to produce a unique 256-bit hash value. The hash value is unique to the input message, so even small changes to the message will result in a completely different hash value. This makes it difficult for attackers to tamper with the message without being detected, as any changes they make will be reflected in the hash value.
Is SNEFRU256 Secure?
One of the key features of SNEFRU256 is that it is resistant to collision attacks, which are a type of attack where an attacker attempts to find two different input messages that produce the same hash value. This is important because it means that it is very difficult for an attacker to create two different messages that have the same hash value, which makes it harder for them to forge messages or tamper with data.
Where SNEFRU256 is used for?
SNEFRU256 is not as widely used as some other hash functions, such as SHA-256 or MD5, but it is still used in some applications where fast and secure hashing is required.