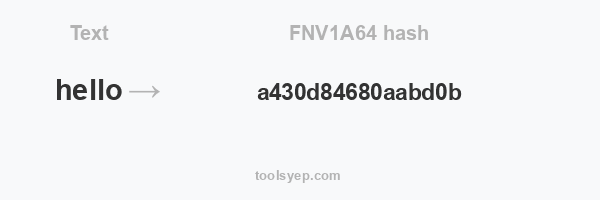
This online tool allows you to generate the hash fnv1a64 of any string.
FNV1A64 length is 16 characters
Hash available
MD2 Hash, MD4 Hash, MD5 Hash, SHA1 Hash, SHA224 Hash, SHA256 Hash, SHA384 Hash, SHA512/224 Hash, SHA512/256 Hash, SHA512 Hash, SHA3-224 Hash, SHA3-256 Hash, SHA3-384 Hash, SHA3-512 Hash, RIPEMD128 Hash, RIPEMD160 Hash, RIPEMD256 Hash, RIPEMD320 Hash, WHIRLPOOL Hash, TIGER128,3 Hash, TIGER160,3 Hash, TIGER192,3 Hash, TIGER128,4 Hash, TIGER160,4 Hash, TIGER192,4 Hash, SNEFRU Hash, SNEFRU256 Hash, GOST Hash, GOST-CRYPTO Hash, ADLER32 Hash, CRC32 Hash, CRC32B Hash, CRC32C Hash, FNV132 Hash, FNV1A32 Hash, FNV164 Hash, FNV1A64 Hash, JOAAT Hash, HAVAL128,3 Hash, HAVAL160,3 Hash, HAVAL192,3 Hash, HAVAL224,3 Hash, HAVAL256,3 Hash, HAVAL128,4 Hash, HAVAL160,4 Hash, HAVAL192,4 Hash, HAVAL224,4 Hash, HAVAL256,4 Hash, HAVAL128,5 Hash, HAVAL160,5 Hash, HAVAL192,5 Hash, HAVAL224,5 Hash, HAVAL256,5 Hash,
What is FNV1A hash?
FNV-1a (Fowler-Noll-Vo) is a non-cryptographic hash function that is fast and efficient for hashing short strings and small integers. It was designed to be used as a general-purpose hash function for hashing data in non-cryptographic applications.
The FNV-1a hash function works by taking a byte-wise representation of the input data, and using a series of bitwise operations to mix the bits of the input data together to produce a hash value. The specific algorithm used in FNV-1a is as follows:
- Initialize a hash value ’h’ to a fixed prime value (for FNV-1a, this value is 2^40 + 2^8 + 0xb3).
- For each byte ’b’ in the input data:
- Multiply ’h’ by the FNV prime value (for FNV-1a, this value is 2^24 + 2^8 + 0x93).
- XOR ’h’ with the byte ’b’.
- Return ’h’ as the hash value.
The FNV prime value is chosen such that it is a large prime number, and the bitwise operations used in the algorithm are designed to efficiently mix the bits of the input data together. This makes the FNV-1a hash function resistant to collision attacks, which are attacks that attempt to find two different inputs that produce the same hash value.
FNV-1a is a variant of the original FNV hash function, and is generally considered to be more robust and efficient than the original FNV hash. It is widely used in various applications, including file systems, databases, and networking protocols.
What is the difference between FNV1A and FNV1A64?
FNV1A64 is simply the 64-bit version of the FNV-1a hash function. This means that the hash value produced by the function is a 64-bit integer, rather than a smaller value. This allows the FNV1A64 hash function to produce a larger range of hash values, making it more resistant to collision attacks. However, it also means that the function may be less efficient than the 32-bit version of the FNV-1a hash function, as it requires more bits to be processed and stored.