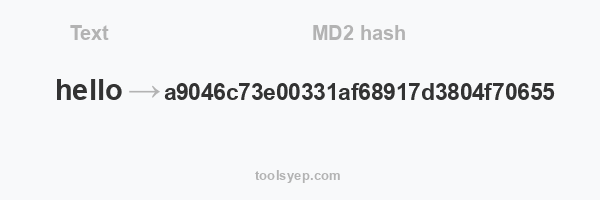
This online tool allows you to generate the hash md2 of any string.
MD2 length is 32 characters
Hash available
MD2 Hash, MD4 Hash, MD5 Hash, SHA1 Hash, SHA224 Hash, SHA256 Hash, SHA384 Hash, SHA512/224 Hash, SHA512/256 Hash, SHA512 Hash, SHA3-224 Hash, SHA3-256 Hash, SHA3-384 Hash, SHA3-512 Hash, RIPEMD128 Hash, RIPEMD160 Hash, RIPEMD256 Hash, RIPEMD320 Hash, WHIRLPOOL Hash, TIGER128,3 Hash, TIGER160,3 Hash, TIGER192,3 Hash, TIGER128,4 Hash, TIGER160,4 Hash, TIGER192,4 Hash, SNEFRU Hash, SNEFRU256 Hash, GOST Hash, GOST-CRYPTO Hash, ADLER32 Hash, CRC32 Hash, CRC32B Hash, CRC32C Hash, FNV132 Hash, FNV1A32 Hash, FNV164 Hash, FNV1A64 Hash, JOAAT Hash, HAVAL128,3 Hash, HAVAL160,3 Hash, HAVAL192,3 Hash, HAVAL224,3 Hash, HAVAL256,3 Hash, HAVAL128,4 Hash, HAVAL160,4 Hash, HAVAL192,4 Hash, HAVAL224,4 Hash, HAVAL256,4 Hash, HAVAL128,5 Hash, HAVAL160,5 Hash, HAVAL192,5 Hash, HAVAL224,5 Hash, HAVAL256,5 Hash,
What is MD2?
The MD2 Hash Generator is based on the MD2 algorithm, a cryptographic hash function created by Ronald Rivest in 1989. It is a fixed-length hash function, which means that the output (or "digest") is always 128 bits, regardless of the size or length of the input. MD2 is similar to MD4 and MD5, which are also hash functions created by Rivest.
How does MD2 hash works?
The MD2 hashing algorithm works by taking an input (or "message") and processing it through a series of mathematical operations. The input can be of any length, but the output (or "digest") is always 128 bits.
The algorithm uses a set of 8-bit operations and logical functions, including modular addition and bit rotation, to transform the input into the output. It also uses a fixed set of 64 bytes, known as the "padding", which is added to the end of the input to ensure that the input is a multiple of 16 bytes.
The algorithm starts by initializing a set of 16 8-bit registers, known as "state". The input is then processed in blocks of 16 bytes, and the state is updated after each block. The state is also used to generate the final output, which is the 128-bit digest.
Overall, MD2 uses a combination of simple operations and a specific padding strategy to create a fixed-length output that should be unique for a given input. However, it is not recommended for new systems due to weak security.
Difference between MD2 and MD5
MD2 and MD5 are both cryptographic hash functions created by Ronald Rivest, but they have some important differences:
Security: MD5 is considered more secure than MD2. MD5 has been around for longer and has undergone more security analysis, which has revealed some weaknesses. MD2 is considered to be less secure than MD5.
Speed: MD5 is faster than MD2. MD2 is slower than MD5 because it uses a slightly more complex algorithm.
Collision resistance: MD5 is more collision-resistant than MD2. A collision occurs when two different inputs produce the same output. MD5 is designed to make it more difficult to find two inputs that produce the same output.
Output: Both MD2 and MD5 produce a 128-bit digest, but the algorithm used to produce the digest is different.
Use: MD5 is more widely used than MD2. Due to the security issues, MD2 is not recommended for new systems and has been superseded by other hash functions such as SHA-256 and SHA-3.
Overall, MD5 is considered to be a stronger and more widely used alternative to MD2.
Difference between MD2 and MD4
MD2 and MD4 are both cryptographic hash functions created by Ronald Rivest, but they have some important differences:
Security: MD4 is considered less secure than MD2. MD4 has been found to have weaknesses, and is not recommended for use in new systems.
Speed: MD4 is faster than MD2. MD4 is designed to be faster than MD2 by using a simpler algorithm.
Collision resistance: Both MD4 and MD2 are not collision-resistant. A collision occurs when two different inputs produce the same output. MD4 and MD2 are not designed to make it difficult to find two inputs that produce the same output.
Output: Both MD2 and MD4 produce a 128-bit digest, but the algorithm used to produce the digest is different.
Use: MD4 is not recommended for use in new systems, due to security weaknesses. MD2 is also not recommended for new systems and has been superseded by other hash functions such as SHA-256 and SHA-3.
Overall, MD4 is considered to be less secure and less widely used than MD2, and neither of them is recommended for new systems.
| Pros | Cons |
|---|---|
| Faster than other hashing algorithms. | Not as widely used as other hashing algorithms. |
| More secure than other hashing algorithms. | It can be susceptible to collisions. |