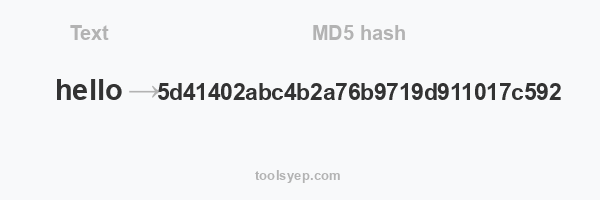
This online tool allows you to generate the hash md5 of any string.
MD5 length is 32 characters
Hash available
MD2 Hash, MD4 Hash, MD5 Hash, SHA1 Hash, SHA224 Hash, SHA256 Hash, SHA384 Hash, SHA512/224 Hash, SHA512/256 Hash, SHA512 Hash, SHA3-224 Hash, SHA3-256 Hash, SHA3-384 Hash, SHA3-512 Hash, RIPEMD128 Hash, RIPEMD160 Hash, RIPEMD256 Hash, RIPEMD320 Hash, WHIRLPOOL Hash, TIGER128,3 Hash, TIGER160,3 Hash, TIGER192,3 Hash, TIGER128,4 Hash, TIGER160,4 Hash, TIGER192,4 Hash, SNEFRU Hash, SNEFRU256 Hash, GOST Hash, GOST-CRYPTO Hash, ADLER32 Hash, CRC32 Hash, CRC32B Hash, CRC32C Hash, FNV132 Hash, FNV1A32 Hash, FNV164 Hash, FNV1A64 Hash, JOAAT Hash, HAVAL128,3 Hash, HAVAL160,3 Hash, HAVAL192,3 Hash, HAVAL224,3 Hash, HAVAL256,3 Hash, HAVAL128,4 Hash, HAVAL160,4 Hash, HAVAL192,4 Hash, HAVAL224,4 Hash, HAVAL256,4 Hash, HAVAL128,5 Hash, HAVAL160,5 Hash, HAVAL192,5 Hash, HAVAL224,5 Hash, HAVAL256,5 Hash,
What Is MD5 Hash
Nouman Khizar
Digital privacy is now a most critical issue than ever before. Therefore, it’s essential to educate people about it. We have seen increasing interest of people in encryption algorithms because they want to improve digital privacy. MD5 is a successor to the MD4 algorithm, and it is the first hashing algorithm to appear on stage globally. Undoubtedly, security vulnerabilities will increase in the future so that MD5 can work in many environments. So, here we’ll discuss almost everything about MD5.
What Is Hashing?
In simple words, it’s a process of converting general information string into an intricate piece of data. It’s done to make the original value or information completely different. In hashing, the hash function converts data into an unrecognizable format. Now you might think, what is a hash function? It’s a mathematical calculation set that converts original information into hashed values. This hash value is known as digest or hash-digest.
What Is MD5 Hash?
MD stands for Message Digest. It’s a hashing algorithm that accepts a message of any length as input and delivers a fixed-length digest value as an output. The idea is to authenticate the original message.
An MD5 hash isn’t encryption. Then what is it? It’s a simple fingerprint of the provided input. Moreover, it’s a one-way transaction, so you can reverse engineer the MD5 hash to get the original string.
Initially, the MD5 hash function was designed to be used as a secure cryptographic hash algorithm to authenticate digital signatures. But now, it has many use cases that we’ll discuss later. Mainly, MD5 can help verify data integrity and detect unintended data corruption.
How Does MD5 Work?
MD5 hashing algorithm processes data in 512-bit strings and breaks it down into 16 words. Each word is composed of 32 bits. The output you get from this hashing algorithm is a 128-bit digest value.
It’s essential to note that the computation of the MD5 digest value isn’t done in one stage. In fact, it’s done in separate stages, and each stage processes 512-bit data along with the digest value computed in the previous stage.
The first stage starts with consecutive hexadecimal numerical values. Moreover, each stage has four message-digest passes. The role of these passes is to manipulate the values in the current data block and also change the values from previous blocks.
The value that is computed from the last block is called the MD5 digest for that block. That is how MD5 works.
Characteristics of the MD5 Algorithm
- MD5 is also known as hash functions, and they’re one-way functions. This is the reason they’re difficult or impossible to reverse.
- You can give input as a message or information of any size, but the output will have a fixed-length message digest.
- Ronald Rivest created this algorithm, and it’s the third one created by him. MD2, MD3, and MD5 all have similar structures.
- MD2 was for 8-bit machines, but MD3 and MD5 are designed for 32-bit machines. MD5 is an extension of MD4 because MD4 was found to be insecure after critical review.
- MD5 isn’t as fast as MD4; therefore, it provides more assurance of data security.
- It’s not possible to guess the input value from a hash function by just looking at its output.
What Is MD5 Used for?
As mentioned earlier, it’s used for various cases. The major use of this hash algorithm is password storage. Many databases are insecure; therefore, people store their passwords in this manner. Linux systems use MD5 hashing algorithms to store passwords securely.
Another use of MD5 is a checksum for files. Nowadays, there are various insecurities in websites, and hackers use them to change download links. Moreover, they trap users into downloading a tempered file. But the use of checksums can help mitigate these insecurities.
A unique hash for a file is generated, and the user may generate a hash based on the file they download. When they compare it, if it matches the original hash, it means the file isn’t tempered. Earlier, it was only used for encryption and data security, but now its primary usage is authentication.
This MD5 hash generator can encode credit card numbers, passwords, and sensitive information into MySQL or other databases like Postgress. So, it’s a handy resource and online tool for ASP programmers, PHP programmers, and anyone developing on SQL, MySQL, Postgress, or any similar platform.
Advantages of MD5
Now, you’re familiar with how MD5 works and its uses. Let’s find out some advantages of MD5.
Low Resource Consumption
It can integrate multiple services into the same framework. Therefore, it doesn’t cause much CPU overhead. Moreover, it has a relatively low memory footprint.
Storing Passwords Is Convenient
When passwords are stored in plaintext format, they can be easily accessible by malicious actors and hackers. Therefore, they shouldn’t be stored in this format. Digest value passwords are secure, and storing these passwords in databases is secure and convenient.
- Easy to Compare Small Hashes
Verifying the digests isn’t easy in the latest hash algorithm families. But it produces 32 digit digest than can be easily compared.
- Integrity Check
With MD5, it’s easy to monitor file corruption. You just need to compare hash values before and after transit. When the hash values are the same, it means the integrity checks are valid. More importantly, it avoids data tempering and corruption.
- Enhance Security
MD5 can help prevent security breaches and hacking in web applications. It’s done by enhancing the security of applications.
Frequently Asked Questions (FAQs) About MD5
People often ask the following questions about MD5.
How Many Bytes Are Present in MD5 Hash?
A single MD5 hash has 16 bytes. Moreover, it looks like 32 numbers and letters. Each digit represents 4 bits. The total bit count of the MD5 hash is 128 bits. Two hexadecimal characters form a byte. Therefore, 32 hexadecimal characters are equal to 16 bytes. Moreover, the length of the MD5 hash will always be 128-bit.
What Is Padding?
It’s a process where a single letter is converted into 32 character output and forms a part of the hash calculation. In case the data doesn’t match the required length to start the MD5 calculation, bits are added. They can help reach a multiple of 512 bits.
What Is the Difference Between MD4 and MD5?
MD4 hash calculation wasn’t complex. Therefore it was not considered secure. But MD4 and MD5 hashes match each other. To increase the complexity, many steps were added to the calculation.
Is MD5 Secure?
For many years, MD5 was a secure option, but now it’s not secure enough for data encryption and cryptographic purposes. The main reason is it is no longer complex now. Due to the evolution in technology, computers have become powerful and can crack MD5. Therefore, a new standard is needed now, and it should be more complex and difficult to crack. But it doesn’t mean that MD5 is useless. You can still use it for many cases, and we have mentioned some use cases of MD5 earlier in this post.
Why MD5 Is No Longer Recommended for Use?
As mentioned earlier, it’s not complex enough now, and computers are more powerful so that MD5 hash can be easily cracked. That’s why people don’t recommend it. Otherwise, you can still use it for some applications like checksum of files and storing sensitive information in different databases.
Which Is Better, MD5 or SHA?
A hashing algorithm must be complex, but it shouldn’t be too complex to become difficult to use. Meanwhile, it shouldn’t be too simple so that anyone can crack or break it. Unfortunately, collisions in MD5 are easy to attain. Therefore, the Secure Hash Algorithm (SHA) addresses the vulnerabilities of MD5. The output of SHA is a long string of hexadecimal characters. When the number of bits increases, it increases the complexity. It’s the main reason SHA is more secure and better than MD5. But MD5 is still a valuable tool for data verification.
What Is the Best Hashing Algorithm?
It’s not easy to say which hashing algorithm is best because they are different and better from each other in terms of use and applications. After the above discussion, it seems that MD5 doesn’t have the best security, but when you create a hash from a secure website, it can be trusted as well. MD5 is a convenient solution for software vendors because it calculates faster than SHA. On the other hand, SHA-256 is the best option for data encryption and website authentication.
Conclusion
Security breaches are also increasing as technology is getting smart and computers are becoming more powerful. Therefore, something was required to counter this issue. Hashing algorithms are perfect options for preventing security breaches and hacker attacks. Hashing algorithms like MD5 can be used for many applications.
Undoubtedly, there are some concerns about its security because it’s not as complex as it should be. But still, it’s an excellent hash function for various applications.