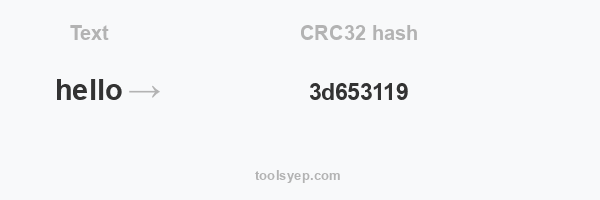
This online tool allows you to generate the hash crc32 of any string.
CRC32 length is 8 characters
Hash available
MD2 Hash, MD4 Hash, MD5 Hash, SHA1 Hash, SHA224 Hash, SHA256 Hash, SHA384 Hash, SHA512/224 Hash, SHA512/256 Hash, SHA512 Hash, SHA3-224 Hash, SHA3-256 Hash, SHA3-384 Hash, SHA3-512 Hash, RIPEMD128 Hash, RIPEMD160 Hash, RIPEMD256 Hash, RIPEMD320 Hash, WHIRLPOOL Hash, TIGER128,3 Hash, TIGER160,3 Hash, TIGER192,3 Hash, TIGER128,4 Hash, TIGER160,4 Hash, TIGER192,4 Hash, SNEFRU Hash, SNEFRU256 Hash, GOST Hash, GOST-CRYPTO Hash, ADLER32 Hash, CRC32 Hash, CRC32B Hash, CRC32C Hash, FNV132 Hash, FNV1A32 Hash, FNV164 Hash, FNV1A64 Hash, JOAAT Hash, HAVAL128,3 Hash, HAVAL160,3 Hash, HAVAL192,3 Hash, HAVAL224,3 Hash, HAVAL256,3 Hash, HAVAL128,4 Hash, HAVAL160,4 Hash, HAVAL192,4 Hash, HAVAL224,4 Hash, HAVAL256,4 Hash, HAVAL128,5 Hash, HAVAL160,5 Hash, HAVAL192,5 Hash, HAVAL224,5 Hash, HAVAL256,5 Hash,
What is CRC32 hash?
CRC32 (Cyclic Redundancy Check 32) is a checksum algorithm that is widely used to detect errors in data transmission and storage. It was developed by Wesley Peterson in 1961, and it is based on the idea of using a polynomial division to calculate a checksum value for a message or file.
A checksum is a value that is calculated based on the data in a message or file, and it is used to detect errors in the data. If the data is transmitted or stored and then retrieved, the checksum can be recalculated and compared to the original checksum to determine whether any errors have occurred.
How CRC32 hash function works?
The CRC32 algorithm operates by taking an input message and dividing it by a predetermined polynomial using a process called polynomial division. The result of the division is a 32-bit checksum value, which is unique to the input message. If the data is transmitted or stored and then retrieved, the checksum can be recalculated and compared to the original checksum to detect any errors that may have occurred.
What is CRC32 used for?
CRC32 is a widely-used checksum algorithm because it is relatively simple to implement and it provides a good level of error detection. It is used in a variety of applications, including data transmission, storage, and error correction.