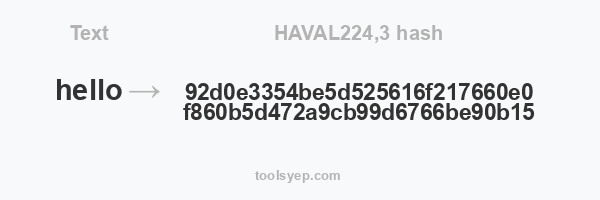
This online tool allows you to generate the hash haval224,3 of any string.
HAVAL224,3 length is 56 characters
Hash available
MD2 Hash, MD4 Hash, MD5 Hash, SHA1 Hash, SHA224 Hash, SHA256 Hash, SHA384 Hash, SHA512/224 Hash, SHA512/256 Hash, SHA512 Hash, SHA3-224 Hash, SHA3-256 Hash, SHA3-384 Hash, SHA3-512 Hash, RIPEMD128 Hash, RIPEMD160 Hash, RIPEMD256 Hash, RIPEMD320 Hash, WHIRLPOOL Hash, TIGER128,3 Hash, TIGER160,3 Hash, TIGER192,3 Hash, TIGER128,4 Hash, TIGER160,4 Hash, TIGER192,4 Hash, SNEFRU Hash, SNEFRU256 Hash, GOST Hash, GOST-CRYPTO Hash, ADLER32 Hash, CRC32 Hash, CRC32B Hash, CRC32C Hash, FNV132 Hash, FNV1A32 Hash, FNV164 Hash, FNV1A64 Hash, JOAAT Hash, HAVAL128,3 Hash, HAVAL160,3 Hash, HAVAL192,3 Hash, HAVAL224,3 Hash, HAVAL256,3 Hash, HAVAL128,4 Hash, HAVAL160,4 Hash, HAVAL192,4 Hash, HAVAL224,4 Hash, HAVAL256,4 Hash, HAVAL128,5 Hash, HAVAL160,5 Hash, HAVAL192,5 Hash, HAVAL224,5 Hash, HAVAL256,5 Hash,
What is HAVAL224,3 hash?
HAVAL is a cryptographic hash function that was first proposed in 1992 by Yuliang Zheng, Josef Pieprzyk, and Jennifer Seberry. It was designed to be a fast and secure hash function, with several different versions being defined depending on the length of the hash value and the number of passes (also known as "rounds") used in the hashing process.
HAVAL224,3 is a specific variant of HAVAL that produces a hash value of 224 bits (28 bytes) in length and uses 3 rounds of hashing. It is considered to be relatively secure, but it is no longer widely used due to the availability of more secure and efficient hash functions.
To compute a HAVAL224,3 hash value, the input message is first padded to a multiple of 32 bits (4 bytes). The padded message is then split into a series of 32-bit words, which are processed through the HAVAL hashing function using 3 rounds of hashing. The final hash value is then produced by concatenating the intermediate hash values produced by each round of hashing.
As with all cryptographic hash functions, HAVAL224,3 is designed to be a one-way function, meaning that it is computationally infeasible to find an input message that produces a given hash value or to find two different input messages that produce the same hash value. This makes it useful for applications such as digital signatures, message authentication, and data integrity checks.