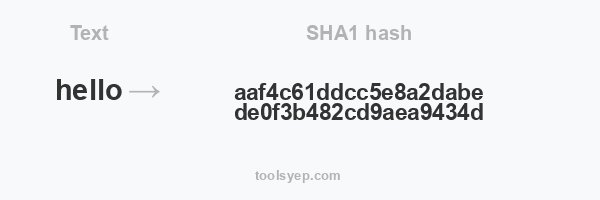
This online tool allows you to generate the hash sha1 of any string.
SHA1 length is 40 characters
Hash available
MD2 Hash, MD4 Hash, MD5 Hash, SHA1 Hash, SHA224 Hash, SHA256 Hash, SHA384 Hash, SHA512/224 Hash, SHA512/256 Hash, SHA512 Hash, SHA3-224 Hash, SHA3-256 Hash, SHA3-384 Hash, SHA3-512 Hash, RIPEMD128 Hash, RIPEMD160 Hash, RIPEMD256 Hash, RIPEMD320 Hash, WHIRLPOOL Hash, TIGER128,3 Hash, TIGER160,3 Hash, TIGER192,3 Hash, TIGER128,4 Hash, TIGER160,4 Hash, TIGER192,4 Hash, SNEFRU Hash, SNEFRU256 Hash, GOST Hash, GOST-CRYPTO Hash, ADLER32 Hash, CRC32 Hash, CRC32B Hash, CRC32C Hash, FNV132 Hash, FNV1A32 Hash, FNV164 Hash, FNV1A64 Hash, JOAAT Hash, HAVAL128,3 Hash, HAVAL160,3 Hash, HAVAL192,3 Hash, HAVAL224,3 Hash, HAVAL256,3 Hash, HAVAL128,4 Hash, HAVAL160,4 Hash, HAVAL192,4 Hash, HAVAL224,4 Hash, HAVAL256,4 Hash, HAVAL128,5 Hash, HAVAL160,5 Hash, HAVAL192,5 Hash, HAVAL224,5 Hash, HAVAL256,5 Hash,
Sha1 Hash Code Generator
Nouman Khizar
The hash code generator is excellent for generating hash codes without hassle. Encode files and massive datasets with a sha1 hash generator.
The hash code generator will make encoding much easier! Your passwords and credit card pins would be perfectly secured by using this hash generator. However, if you have a lot of data to encode, then your choice should be the sha1 hash generator, and here is all you need to know about it! But before heading to it, you need to understand the concept of a hash generator!
What Is a Hash Generator?
Encoding your credentials is one of the best ways to save you from digital theft. We all know that digital crime is gaining a boost, and keeping passwords in your mobile and diary could lead you to a significant loss! But a hash generator is a perfect solution to all these problems. You can store this data in MySQL, SQL, and other scripting software to ensure complete data privacy!
Also, hashing is being used to secure transactions and provide a safe file transfer; the opportunities are endless! Using this tool will ensure data integrity and security and avoid data manipulation.
Want to know the science behind it? Well, here is all you need to know!
A hash generator helps to encode your codes into different symbols, and now you have a unique string that no one will ever know! For example: Write “Maddy” in the hash generator box, and now the output would be a character string like this below:
“94b151809b54b41b380ad72f0a676beb1864ad03”
Would anyone be able to find out what the dataset was? The answer is “No”; however, only the person who can decode this can find the actual data. That’s why encryption or encoding your data is one of the best solutions to your problems!
One of the most effective hash generators is the sha1 hash generator because it will take you to a world of privacy! The section above explains the hash generator; now, let’s explore the sha1 hash generator.
What Is the SHA1 Hash Generator?
The purpose of the sha1 hash generator is similar to the MD5 hash generator, but the difference is that the output here is a 160-bit hash value. This value is called the message digest. The values are compressed using the hexadecimal format.
But why should you consider the sha1 hash generator over others? The answer is simple. The sha1 generator profoundly works to convert your files into encrypted files so that no one can add malicious data or links to your file while transferring them. You can easily verify your file by using the sha1 hash-generated value.
To verify your file, you need to add a checksum before transferring it and check the hash value once it reaches the destination source.
Different hash formats are available for encoding data
Find them out here.
The sha1 hash generator would become your best friend because it is also adequately used for file encryption so that you can encrypt and transfer your files without the fear of leaking information. Now privacy is at your fingertips!
Also, try out the Password generator!
It would help if you tried the sha1 hash generator to avoid data discrepancies and work in a safe environment. Encoding passwords and files is especially necessary for data security. The best part is that the hash value will be generated within seconds! You will enter the value that needs to be encoded; that’s it! You have your encoded value! Also, this tool is a free hash generator tool and would cost you nothing!
How Does the Sha1 Hash Generator Work?
The sha1 hash generator uses an algorithm that stands for secure hashing algorithm. You can input a variable, and the output tends to be a fixed length. However, this is a cryptographic function that helps to secure and encode data so that the data would not come into the hands of a third party. The algorithm works to transform the data by applying a hash function.
In addition, you can find different types of secure hashing algorithms: Sha0, sha1, sha2, sha3, sha256, etc. Sha2 and sha256 are the same and refer to the same hashing function. The output of this hash function would be a 256-bit rather than a 160-bit, and it tends to be a more secure and fool-proof version of a hash generator. Try out these hash generators and get ultimate security like never before!
Pros & Cons of the Sha1 Hash Generator
Pros
- It is easy to use.
- It gives a secure file transfer.
- Most people use it to save passwords and credit card pins.
Cons
The hash value is easy to compute, which means that a third party can evaluate the password, but they would need to spend a hefty amount.
Use the Sha1 Hash Generator Today!
The sha1 hash generator is a perfect way to encrypt your files and data to prevent secret information from intruders. If you are a company or an organization, you will need data encryption to stay ahead of your competitors, and this tool is the best way to do so!
Some popular companies like Google do not prefer using this hash generator to avoid hash collisions. However, the third party would need to spend a lot of money to counter and manipulate the file. That’s why you can also opt for a sha2 or sha256 hash generator because it comes with a better response against collision.
Want to Try It?
Again, the sha1 hash generator would be the best thing to use for encoding your data; whether it is passwords or credit card pins, you can keep all your information stored! Also, it is a great way to encode files and transfer data which requires more privacy, giving you complete control over file verification. In this world of cybercrime and digital theft, you need to use efficient ways to enhance the security of your data! The sha1 hash generator is one of the best tools to try.